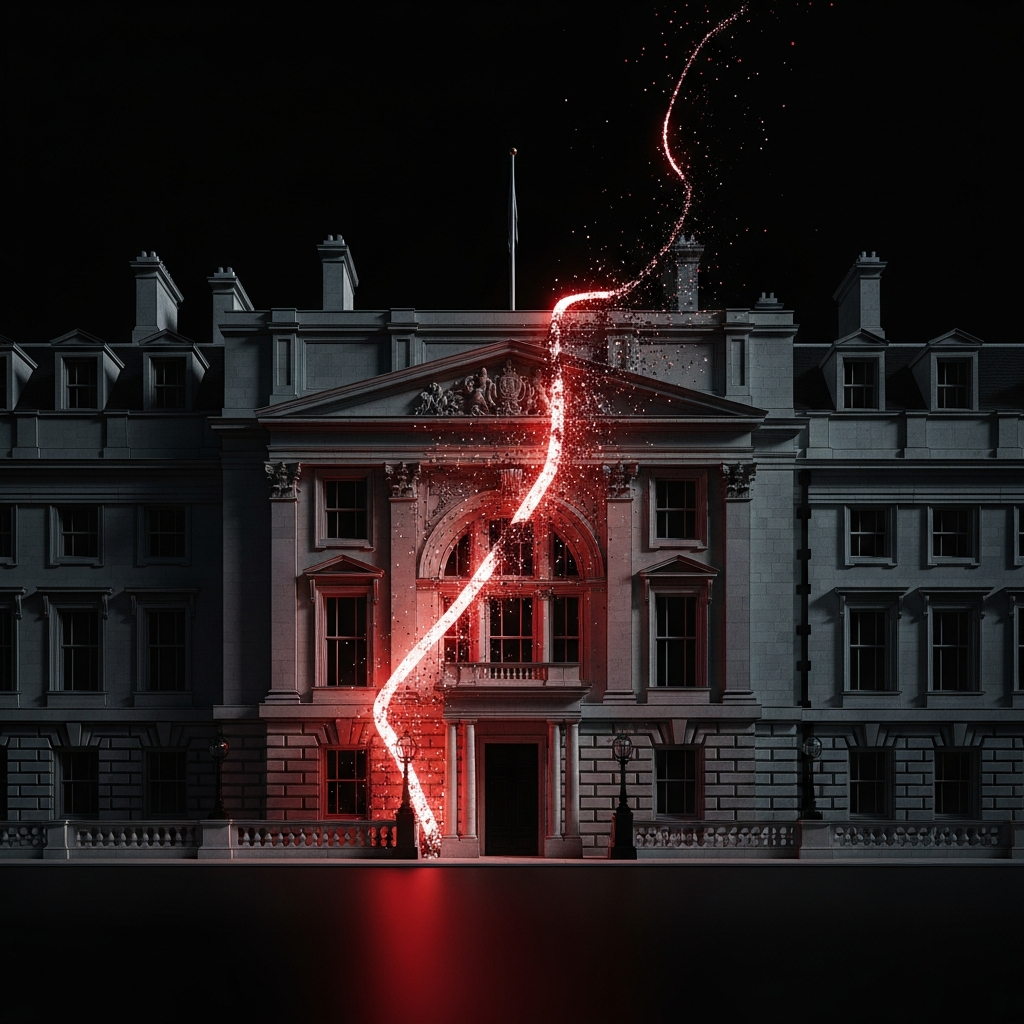
Beyond the Breach: State-Sponsored Espionage and the UK Foreign Office Cyberattack
The recent confirmation of a sophisticated and severe breach at the UK’s Foreign, Commonwealth and Development Office (FCDO) is a stark reminder that the front lines of international conflict are no longer just physical. The UK Foreign Office cyberattack, attributed to the Chinese state-sponsored group Storm-1849, represents a significant event in the ongoing shadow war of digital espionage. This wasn’t a simple smash-and-grab for data; it was a targeted, persistent intrusion aimed at the very heart of Britain’s diplomatic and intelligence apparatus. Understanding this attack requires looking beyond the technical details of the breach and examining the broader context of geopolitical cyber warfare, the motivations of actors like Storm-1849, and the defensive strategies nations and organizations must now adopt to survive.
Unmasking the Assailant: A Profile of Storm-1849
To comprehend the gravity of the FCDO breach, one must first understand the perpetrator. “Storm-1849” is the designation given by Microsoft to a highly sophisticated Advanced Persistent Threat (APT) group. While threat actor names can vary between cybersecurity firms, the consensus in the intelligence community firmly links this group’s activities to the operational directives of the Chinese government.
Who is Storm-1849?
Storm-1849, also associated with groups known as APT31 or “Zirconium,” is not a collection of rogue hacktivists. It is a well-resourced, highly disciplined unit conducting intelligence operations on behalf of the People’s Republic of China. Their objectives are not financial gain, which separates them from common cybercriminal syndicates. Instead, their mission aligns with China’s long-term strategic goals: gathering political, economic, and military intelligence to inform state policy and gain a competitive advantage on the world stage. This is the essence of state-sponsored cyber espionage.
A Patient and Persistent Modus Operandi
The “Persistent” in APT is the key characteristic of groups like Storm-1849. Their approach is methodical and designed for long-term access, not a quick in-and-out raid. Their tactics often include:
- Spear-Phishing: Crafting highly convincing emails, often targeting specific individuals within an organization, to trick them into revealing credentials or deploying initial malware.
- Exploitation of Zero-Day Vulnerabilities: Using previously unknown software flaws to gain an initial foothold, demonstrating a high level of technical capability and resources.
- Living off the Land (LotL): Employing legitimate system tools and processes already present on a network (like PowerShell or WMI) to conduct their activities. This makes their presence extremely difficult to detect, as they blend in with normal network traffic.
- Data Exfiltration: Slowly and quietly siphoning data over extended periods to avoid triggering automated security alerts that look for large, sudden data transfers.
Their goal is to become an invisible, long-term fixture within a target network, observing, learning, and stealing information that serves the strategic interests of the Chinese state.
The Strategic Target: Why the UK Foreign Office?
The choice of the Foreign, Commonwealth & Development Office as a target was no accident. The FCDO is the central nervous system of the UK’s global engagement. Breaching its network is the digital equivalent of placing a listening device inside the cabinet room, providing an adversary with an unparalleled strategic advantage.
A Treasure Trove of Intelligence
The information housed within the FCDO’s systems is of immense value to a foreign power. A successful breach could yield:
- Diplomatic Cables and Communications: Private assessments and candid discussions about foreign leaders, international relations, and UK policy positions.
- Negotiating Strategies: Detailed plans and red lines for critical trade deals, climate summits, and security agreements.
- Intelligence Assessments: Information shared from partner agencies like MI6 and GCHQ regarding global threats and foreign state activities.
- Personal Information: Sensitive data on diplomats, foreign contacts, and potentially UK citizens abroad, which can be used for blackmail or future targeting.
For a geopolitical competitor like China, this information provides a direct line of sight into the UK’s intentions and capabilities, undermining its diplomatic leverage and national security. This is a prime example of the severe impact of government cybersecurity threats.
The Geopolitical Chessboard: Espionage in the 21st Century
The UK Foreign Office cyberattack must be viewed as a single, calculated move in a much larger and more complex geopolitical game. Chinese government hacking is a core component of its strategy to challenge the existing international order and advance its own influence. Cyber operations provide a powerful, deniable, and cost-effective means of achieving state objectives.
Information as the Ultimate Weapon
In this digital Cold War, information is power. The data exfiltrated by the Storm-1849 APT can be weaponized in numerous ways. It allows Beijing to anticipate the UK’s diplomatic moves, counter its arguments in international forums, and gain a significant upper hand in economic negotiations. It can also be used to sow discord among Western allies by selectively leaking sensitive or embarrassing communications, eroding trust within alliances like NATO or the Five Eyes intelligence-sharing network.
Conflict in the “Gray Zone”
State-sponsored cyberattacks exist in a “gray zone” of conflict—an area of confrontation that falls below the threshold of conventional armed conflict. This is a key element of modern geopolitical cyber warfare. A state can conduct extensive espionage operations, disrupt critical infrastructure, or run influence campaigns without triggering a military response. This persistent, low-level conflict allows nations to continually jockey for position and weaken their adversaries without firing a single shot, making robust cybersecurity a fundamental pillar of modern national defense.
The Ripple Effect: When Government Breaches Affect the Private Sector
It’s a mistake to believe that an attack on a government ministry is a contained event. The interconnected nature of our digital world means that the shockwaves from the FCDO breach extend far into the private sector. Government departments do not operate in a vacuum; they rely on a vast ecosystem of private contractors, technology suppliers, academic institutions, and consultants.
Supply Chain as a Vector
A compromised government network can serve as a launchpad for attacks against its partners. Attackers like Storm-1849 can exploit the trust and digital connections between a ministry and its suppliers to move laterally into corporate networks. This makes the private companies that support government functions—from defense contractors to IT service providers—high-value secondary targets. Their intellectual property, research data, and client information become vulnerable.
Erosion of Trust and Economic Impact
Repeated, high-profile breaches erode public and international trust in a government’s ability to secure its data. This can have tangible economic consequences, making international partners and investors wary of engaging in sensitive collaborations. It underscores the reality that national cybersecurity and economic security are inextricably linked.
Building a Resilient Defense: A Multi-Layered National Strategy
Responding to the threat posed by groups like Storm-1849 requires more than just better firewalls and antivirus software. It demands a sophisticated, proactive, and multi-layered defensive posture that integrates technology, process, and people.
Proactive Threat Hunting and Intelligence
Organizations can no longer afford to be passive. Instead of waiting for an alarm to sound, security teams must engage in proactive threat hunting—actively searching their networks for the subtle signs of a stealthy intruder. This involves using advanced endpoint detection and response (EDR) tools and leveraging threat intelligence feeds to understand the specific TTPs of adversaries like the Storm-1849 APT.
Adopting a Zero Trust Architecture (ZTA)
The old model of a strong perimeter with a trusted interior is obsolete. A Zero Trust Architecture operates on the principle of “never trust, always verify.” Every user, device, and application must be authenticated and authorized before accessing any resource on the network, regardless of its location. This approach uses micro-segmentation to contain intruders, preventing them from moving laterally across the network even if they breach the initial perimeter.
Strengthening the Human Firewall
Technology alone is not enough. The most common entry point for sophisticated attacks remains human error. Continuous, engaging, and relevant cybersecurity awareness training is critical. Employees must be trained to recognize and report suspicious activity, turning every individual into a part of the organization’s defense system. This goes beyond annual compliance training and involves regular phishing simulations and education on the latest threats.
Frequently Asked Questions (FAQ)
What is Storm-1849?
Storm-1849 is the name given by Microsoft to an Advanced Persistent Threat (APT) group linked to the Chinese government. Also known as APT31 or Zirconium, this group specializes in long-term, stealthy state-sponsored cyber espionage to gather intelligence for the Chinese state.
Why are government departments like the Foreign Office targeted so frequently?
Government ministries like the FCDO are prime targets because they hold highly sensitive data related to national security, foreign policy, and economic strategy. Accessing this information provides an adversary with a significant geopolitical and strategic advantage.
What is the difference between cybercrime and state-sponsored cyber espionage?
The primary difference is motive. Cybercrime is typically financially motivated, involving activities like ransomware, fraud, or theft for monetary gain. State-sponsored cyber espionage is politically motivated, focused on intelligence gathering to support a nation’s strategic, military, or economic objectives.
How can businesses protect themselves from similar state-sponsored threats?
Businesses, especially those in critical sectors or government supply chains, should adopt a defense-in-depth strategy. This includes implementing a Zero Trust framework, conducting proactive threat hunting, providing robust employee training, maintaining strict access controls, and working with expert cybersecurity partners to assess and strengthen their security posture.
What are the likely long-term consequences of the UK Foreign Office cyberattack?
The long-term consequences include heightened diplomatic tensions between the UK and China, a comprehensive review and overhaul of UK government cybersecurity protocols, increased scrutiny on supply chain security, and a greater allocation of resources to national cyber defense capabilities.
Conclusion: The New Imperative for Cyber Resilience
The UK Foreign Office cyberattack is a watershed moment, illustrating with chilling clarity that digital infrastructure is now a primary battleground for international power struggles. The actions of the Storm-1849 APT are not isolated events but part of a sustained campaign of state-sponsored cyber espionage that targets the core functions of government and industry. For both public and private sector organizations, the lesson is clear: cybersecurity is no longer a peripheral IT issue but a central component of organizational survival and national security.
Building resilience against these advanced threats requires a forward-thinking approach that integrates sophisticated technology, intelligent strategy, and human vigilance. Whether you are safeguarding proprietary corporate data, developing secure public-facing applications, or ensuring the integrity of critical systems, the principles of robust cybersecurity are universal.
If you’re ready to move beyond a reactive security stance and build a resilient posture designed for the realities of modern threats, the team at KleverOwl is here to help. Contact our experts today for a comprehensive cybersecurity consultation and learn how our expertise in building secure web and mobile solutions can fortify your digital presence.